MSPbots Bug Bounty Program
1. Purpose
MSPbots operates a multi-tenant platform that processes operational and client-related data. The purpose of this Bug Bounty Program is to identify and remediate security vulnerabilities that could impact:
- Confidentiality of client or tenant data
- Authorization boundaries between users, roles, and tenants
We invite qualified security researchers to responsibly disclose vulnerabilities in accordance with this policy.
2. Authorization & Safe Harbor
Security testing conducted in good faith, within the scope defined below, is considered authorized by MSPbots.
If you:
- Follow this policy
- Avoid privacy violations and service disruption
- Do not access or retain real customer data beyond minimal proof
MSPbots will:
- Not pursue legal action
- Not initiate law enforcement contact
- Treat your findings as confidential security research
This safe harbor does not apply to actions outside scope, malicious activity, or violations of applicable law.
3. In-Scope Assets
3.1 Applications & Services
The following MSPbots-owned assets are in scope unless otherwise stated:
- Web application (app.mspbots.ai)
- Authentication and authorization flows (app.mspbots.ai)
- Multi-tenant isolation mechanisms (app.mspbots.ai)
3.2 Environments
- Production environment only
- Testing must be performed using accounts and tenants owned by the researcher
4. In-Scope Vulnerability Classes
The program prioritizes vulnerabilities that could lead to unauthorized data access or cross-tenant impact, including but not limited to:
4.1 Authentication & Authorization
- Broken access control (IDOR, missing authorization checks)
- Privilege escalation
- Role or permission bypass
- Session fixation or hijacking
4.2 Multi-Tenant Isolation (High Priority)
- Cross-tenant data exposure
- Tenant boundary bypass
Any vulnerability that demonstrates access to data outside the reporter’s tenant is automatically classified as High or Critical severity.
4.3 Data Exposure
- Unauthorized access client metadata
- Excessive data returned by APIs
- Sensitive data exposure via logs, errors, or exports
- Insecure object or file access
4.4 Integrations & Agents
Missing request authentication or signing
5. Out-of-Scope
The following activities and findings are not eligible for rewards:
- Denial of Service (DoS/DDoS), load testing, or traffic flooding
- Automated scanning that degrades platform stability
- Social engineering, phishing, or employee targeting
- Physical security attacks
- Vulnerabilities in third-party services unless directly exploitable through MSPbots
- Self-XSS or issues requiring user cooperation
- Missing headers or best-practice findings without demonstrable security impact
- Attacks requiring malware, root access, or compromised client systems
6. Rules of Engagement
Permitted
- Testing only against accounts and tenants you control
- Manual or low-impact testing techniques
- Minimal data access required to prove impact
- Redacted screenshots or partial payloads as proof
Prohibited
- Accessing or exfiltrating real customer data
- Mass data extraction or scraping
- Persistence mechanisms or backdoors
- Service disruption
- Sharing findings prior to remediation and approval
Researchers must immediately stop testing once unauthorized data access is confirmed.
7. Severity Classification
Severity is determined based on data sensitivity, exploitability, and scope of impact.
| Severity | Description |
|---|---|
| Critical | Cross-tenant data access, auth bypass leading to unrestricted data exposure. |
| High | Unauthorized access to sensitive client data or privileged functionality. |
| Medium | Limited data exposure or logic flaws with constrained impact |
| Low | Minor information disclosure without direct data or security impact |
8. Rewards
Rewards are determined by:
- Severity classification
- Quality and clarity of the report
- Reproducibility and exploit reliability
- Novelty of the finding
Duplicate reports are rewarded only for the first valid submission.
9. Reporting Requirements
All submissions must be submitted to support@mspbots.ai and include:
- Affected asset or feature
- Account role and tenant context used
- Step-by-step reproduction instructions
- Description of data or security impact
- Screenshots or Proof of Concept videos
- Any relevant logs or response samples
Incomplete reports may be delayed or closed.
10. Response & Disclosure Process
- Initial acknowledgment: within 3-5 business days
- Validation and triage based on severity
- Remediation timelines depend on risk and complexity
- Public disclosure requires written approval from MSPbots
We strongly support coordinated disclosure.
11. Compliance Alignment
This Bug Bounty Program supports MSPbots’ compliance and security posture, including:
- SOC 2 (Vulnerability Management & Monitoring)
- GDPR Article 32 (Security of Processing)
- ISO 27001 Secure Development and Operations controls
12. Policy Updates
MSPbots reserves the right to update this policy at any time. Material changes will be communicated via this page or the designated reporting channel.
Ready to Automate Your MSP Operations?
Unlock real-time insights and automation bots that transform how MSPs work.
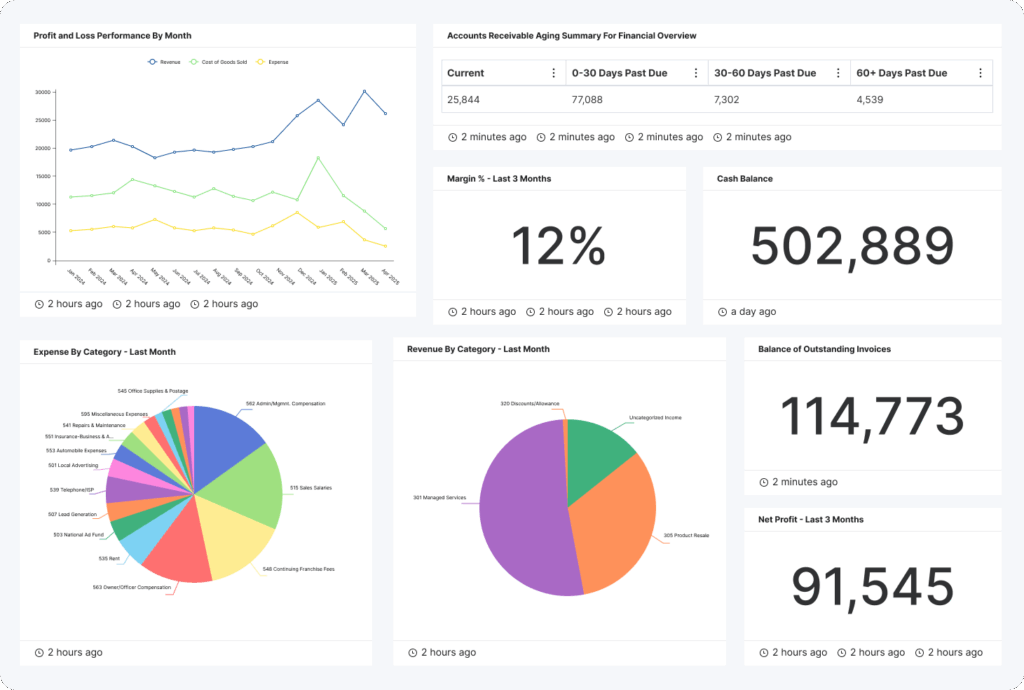
Enterprise-grade everything
Out-of-the-box security with privacy-secured AI.
- 24/7 SUPPORT
SOC 2 TYPE II CERTIFIED
GDPR COMPLIANCE
HIPAA
PCI COMPLIANCE
ADVANCE FIREWALL PROTECTION
2FA SECURITY